What’s new in UserLock 9.5
- Manage and secure access from Mac computers
- New predefined reports
- Detection of conflicting UserLock service installations
- Utilize the description field of computer accounts found in Active Directory
Manage and secure access from Mac computers
UserLock 9.5 now supports both Windows and Mac users.
Regardless of the size of the business, Macs have seen a rapid increase in adoption among enterprise users. To ensure IT can offer access protection to all their users, UserLock 9.5 includes a new agent to support Mac computers.
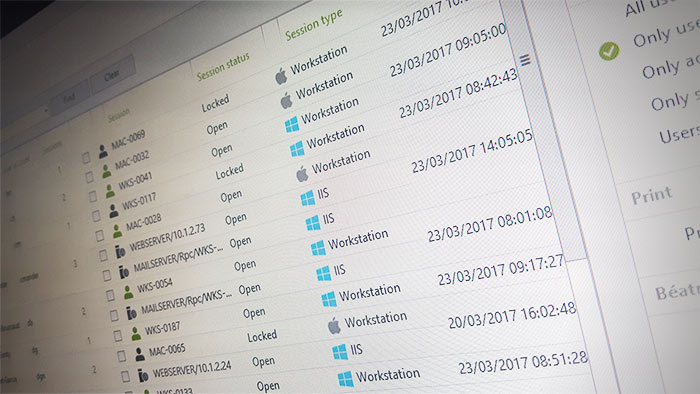
New icons tag sessions to indicate if they are from a Mac or Windows machine.
Supported Mac Versions
UserLock 9.5 supports the latest versions of Mac computers:
- El Capitan (10.11)
- Sierra (10.12)
Mac agent
UserLock has different agents for Windows and Mac computers.
Mac agents can be installed manually on the computers that need to be managed.
Supported Features
The UserLock Mac agent is designed to manage and secure access from Mac workstations. Supported features that apply to any Mac user include:
- Access Control and Protection: Non-intrusive, context-aware access controls customized to define network access conditions. Limit access by location (workstation, IP address, etc.), time, session type or number of simultaneous sessions.
- Access Detection and Response: Real-time monitoring and risk detection tools immediately alert you to suspicious logon activity – so you can take action quickly.
- Access Audit and Report: Record, centralize and audit all network logon events, for comprehensive reports and detailed insights.
New Predefined Reports
UserLock 9.5 offers further options to its built-in reporting.
Generate predefined reports on the following types of access and access attempts:
-
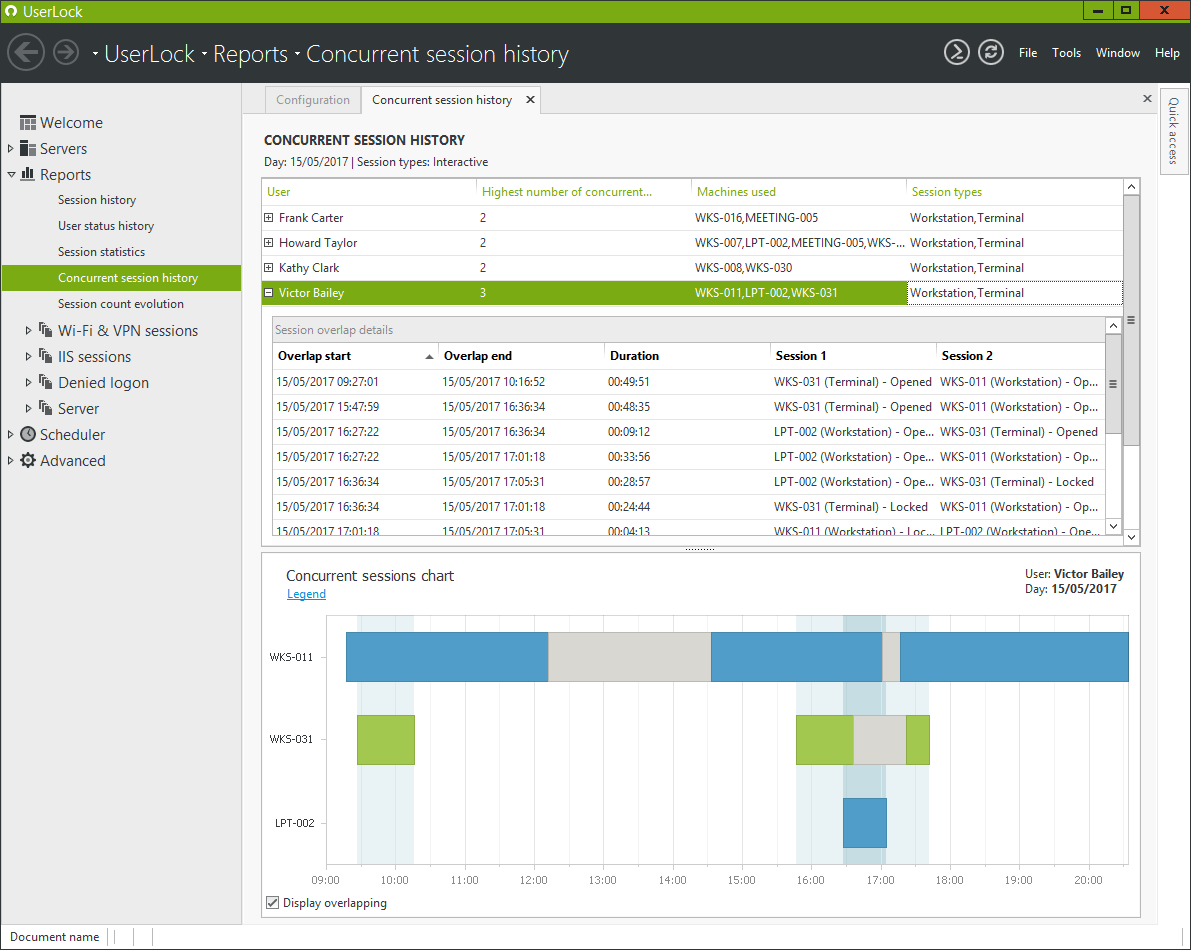
Concurrent Sessions
Report on all domain users with simultaneous sessions opened within a given day.
-
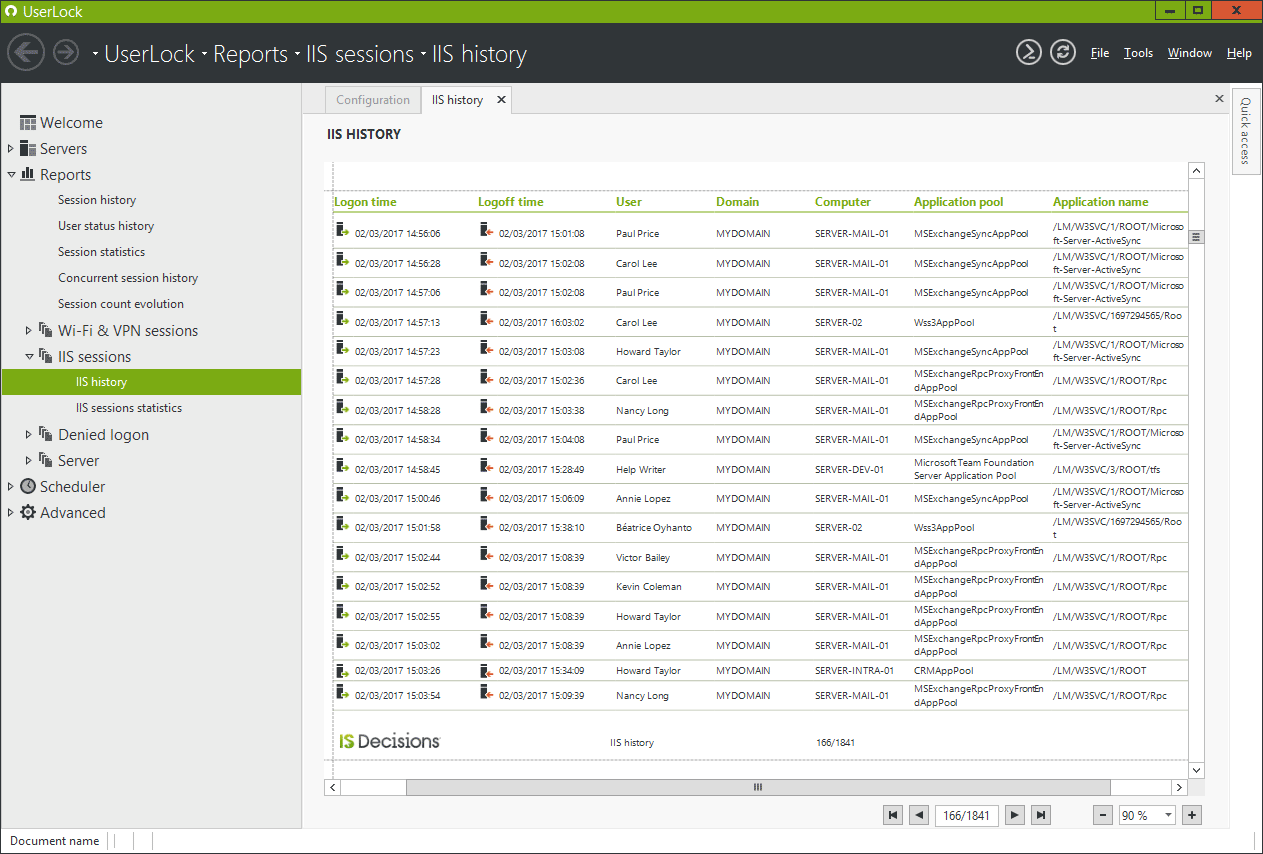
IIS Session Activity
Report on all session history for Microsoft IIS Servers (E.g. Web apps such as Outlook Web Access).
-
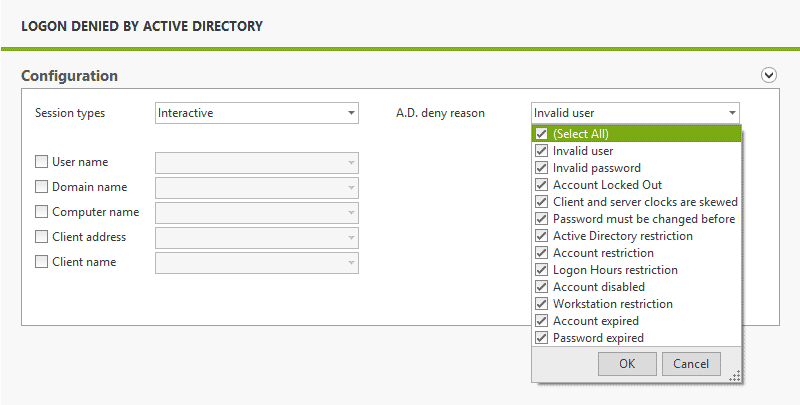
Logons Denied by Active Directory
Report on all access attempts rejected by Windows. This includes multiple logon failure attempts.
-
Logons Denied by UserLock
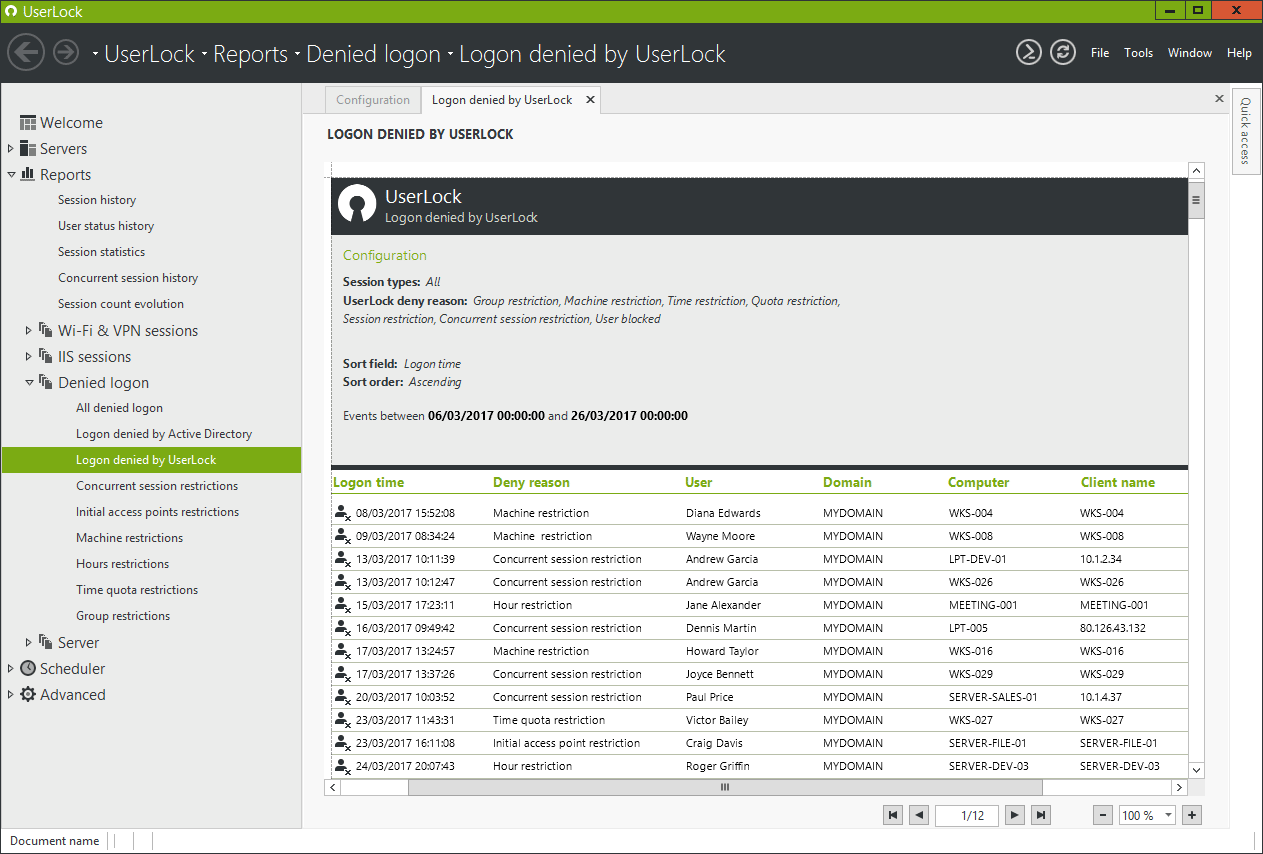
Report on all access attempts rejected by UserLock due to unauthorized:
- Machine or IP address
- Session type
- Timeframe or Quota
- Number of concurrent sessions
- Number of initial access points
Detection of conflicting UserLock service installations
UserLock can now detect and alert administrators to this problem. A conflicting installation can lead to issues with the proper functioning of the UserLock server. For example, a loss of data or customized access policies not being correctly applied.
UserLock will also detail on how best to repair.
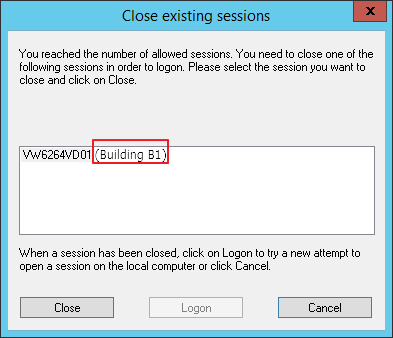
Utilize the description field of computer accounts found in Active Directory
Administrators are now able to access and use the Active Directory description field of a computer account. This can be used as a variable when configuring UserLock’s user messages.
For example in the ‘Welcome Message’, details of a user’s last logon can now include the location (Building B1) of the machine.
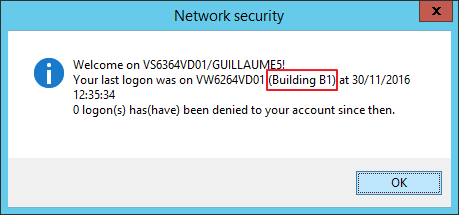
Or when a user is given the choice to close an existing session (this requires the "SessionWithDescription" advanced setting to be activated in the Advanced Settings of UserLock).