MFA & access management
IAM for Active Directory
Secure every logon and session across network and SaaS resources, without rewiring your identity stack. UserLock brings modern identity and access management (IAM) to Active Directory, adding granular multi-factor authentication (MFA), single sign-on (SSO), contextual access controls, and real-time session management.
Modern identity security for Active Directory, minus the complexity
With UserLock, enforce identity security on-premises and extend it seamlessly to the cloud. You can retain sovereignty over sensitive identity data, apply smart access controls, and support compliance beyond box-checking.
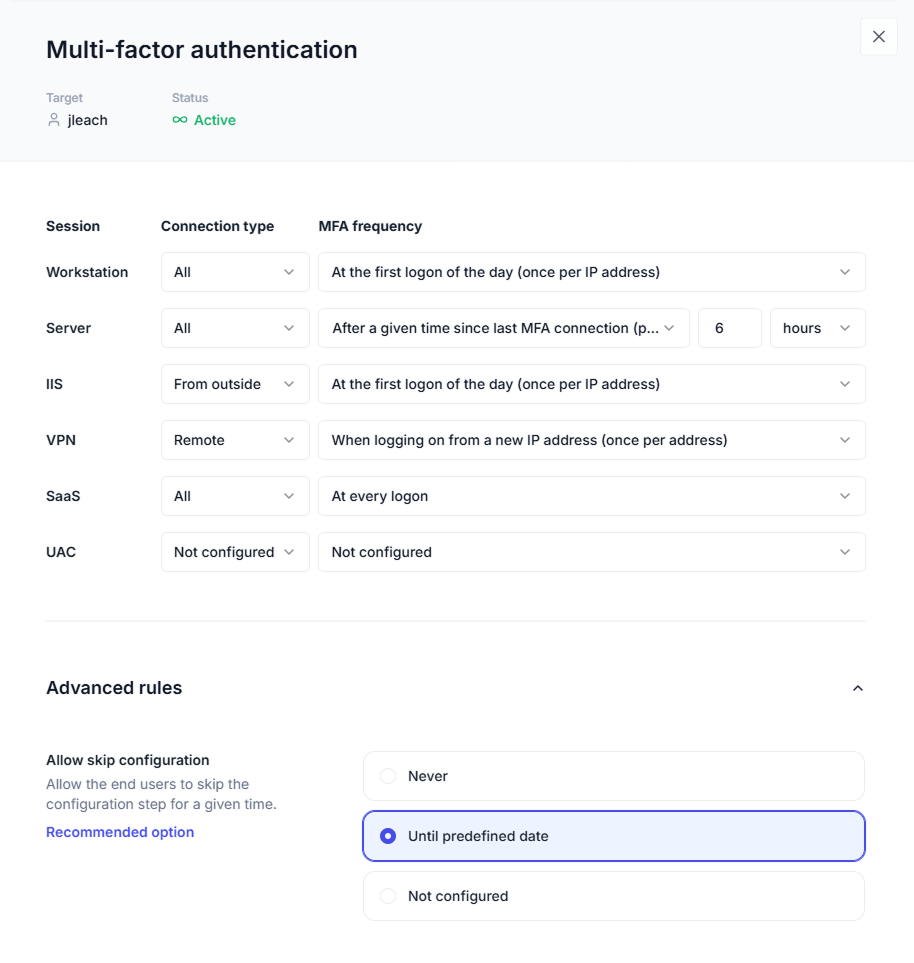
Take control of multi-factor authentication (MFA) implementation
Enable flexible, no-fuss MFA across existing AD users, groups, and organizational units (OUs). Set granular MFA policies by connection and session type to control how often users are prompted based on risk and context.
Apply MFA across all critical access paths, not just at initial logon, but throughout the session, helping prevent credential misuse and lateral movement:
Windows login
Remote Desktop (RDP, RD Gateway, RemoteApp)
IIS (OWA, RDWeb, SharePoint...)
VPN access
SaaS apps (Microsoft 365, AWS, Salesforce...)
Windows UAC prompts
Fully functional in air-gapped networks, as well as offline and off-domain scenarios.

Extend secure authentication to the cloud with single sign-on (SSO)
Pair SSO with MFA to provide secure, one-step access to Microsoft 365 and other SaaS apps after a successful on-prem Active Directory logon.

Layer security using contextual access controls
Apply access controls that stay out of the way for legitimate users and block connections that don’t match your role- and context-based conditions.
Role
Set different access controls based on AD users, groups, and organizational units (OUs).
Origin
Define access based on machine, location, IP address, and more.
Time
Limit access to working hours, set session length limits, or define logon time quotas.
Session type
Manage access across workstation, terminal, Wi-Fi, VPN, IIS, SaaS, Remote Desktop (RDP, RD Gateway, RemoteApp), and VDI sessions.
Simultaneous connections
Limit concurrent sessions and control how many initial access points (concurrent logons) to allow per user, group, or OU.

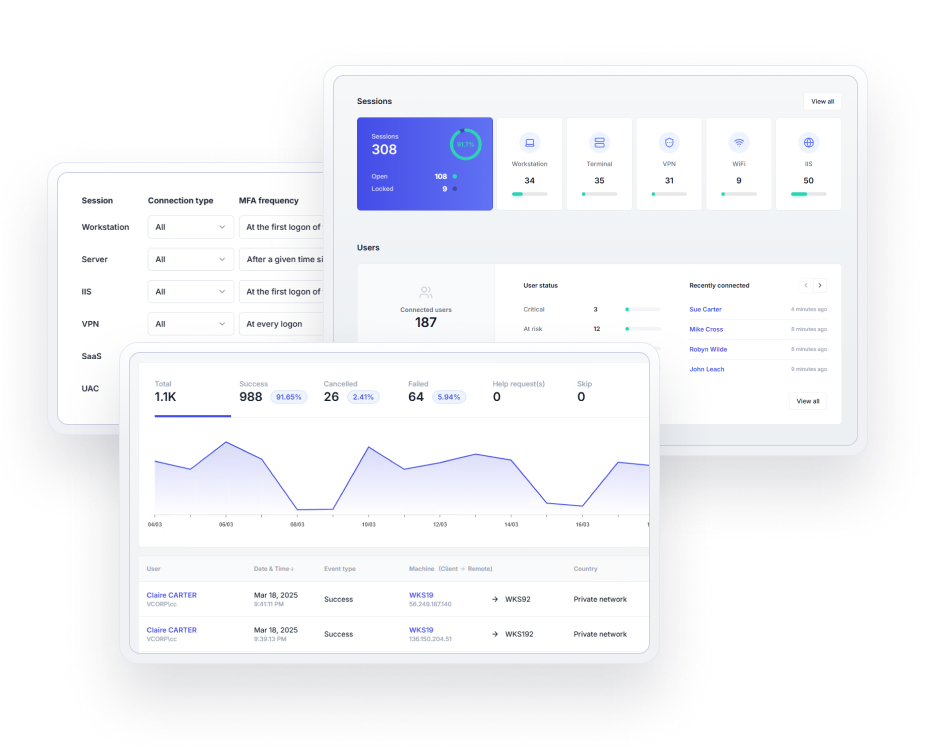
Detect threats with session management
Monitor user access and session activity in real-time, set up alerts, and take immediate action to block or restrict sessions directly from the console.

Ensure full visibility with Active Directory user login auditing
Track and record all Windows user logon events with a searchable, reliable audit across on-prem Active Directory and SaaS access, including failed or denied access attempts.

Support compliance with user and administrator activity reports
Create detailed reports on Active Directory user logon/logoff activity, MFA events, administrator actions, denied logons, and more to help meet compliance requirements and support forensics.
Explore UserLock
UserLock: IAM software for the on-prem-first enterprise
UserLock is one of the few identity and access management solutions purpose-built for seamless integration with on-premises Active Directory.
By layering strong security controls around the AD identity, you can simplify your IAM architecture, control costs, and keep managementoverhead low.
Simplify IT management
Eliminate identity sprawl and cut IT’s workload by managing a single user identity and monitoring one centralized dashboard across all access types.
Enhance security
Close security gaps such as session token theft that arise from fragmented or overly complex identity and access systems.
Keep end users productive
Decide how much security is enough with granular policies per AD user, group, and OU, so access controls protect the business without getting in the way of work.
Why IT teams choose UserLock
Simple to use
Quick to deploy and intuitive to manage, UserLock scales easily to any number of users, with little day-to-day administrative effort from IT.
Non-disruptive
UserLock integrates directly with Active Directory and continuously synchronizes with it, enforcing security controls without introducing identity sprawl or user friction.
Easily adopted
Granular controls let you tailor restrictions that can stop threats without slowing down users.
Cost-effective
Building on your investment in Active Directory, UserLock delivers layered, effective identity security without the cost and overhead of cloud-first IAM platforms.
Affordable, easy to use with Active Directory
UserLock allows us to have one single 2FA solution for all of our users. It integrates easily with Active Directory, and is simple to install and maintain. It’s basically an IT Manager’s dream. ”
Bill Hopkins
City of Keizer
Reviewed on

Simple and reliable.
I've tested several 2FA software. In the end, I stuck with UserLock because it requires no administrative effort. I really like the reports and the control of who is connected to which device. ”
Andreas L.
Reviewed on

Read the case studyAn administrators premier management tool!
In a flash, I can control my users’ login experience, find/identify users computers and remote in for support. It’s just always there for me. I can’t imagine working without it now. ”
Bob B.
Server administrator | Education Management
Reviewed on

Userlock has been a great tool and helped us tighten up our user security.
It's used in conjunction with Active Directory and Group Policy to secure all logon types in the domain. ”
Gov't Network Tech
Reviewed on

What’s new in UserLock
UserLock 13.0 brings a new level of simplicity and control to secure workforce access across on-prem and hybrid Active Directory setups.