Manage SSO for Microsoft using Powershell
This guide explains how to configure or remove Microsoft SSO using PowerShell commands, and how to synchronize users between Entra ID and your local Active Directory. It provides an alternative to the graphical UserLock SSO Assistant, ideal for automated or scripted deployments.
Note
If this is your first time configuring SSO for Microsoft, consult Standard configuration for Microsoft first.
Administrators can manually federate or defederate Entra ID domains using the Microsoft Entra PowerShell modules.
They can also manage users to create or synchronize Entra ID accounts with their local Active Directory.
This approach is ideal for automation, remote configurations, or troubleshooting situations where the graphical interface is unavailable.
Note
PowerShell operations directly modify Entra ID federation settings.
Always verify all values before applying them.
✅️ PowerShell 5.1 or later.
✅️ The Microsoft.Graph powershell module installed.
✅️ Global Admin credentials in your Entra ID tenant.
✅️ Connectivity to Entra ID endpoints.
✅️ A verified domain in Entra ID.
Before running any command, you will always need to connect to Microsoft Graph with the required permissions.
Open a Powershell terminal
Connect to Microsoft Graph
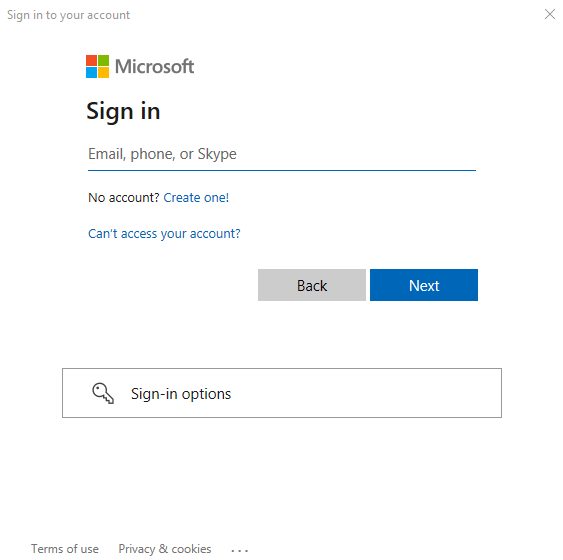
powershellConnect-MgGraph -Scopes "Domain.ReadWrite.All User.ReadWrite.All Directory.ReadWrite.All Directory.AccessAsUser.All"When prompted, sign in with your Entra ID Global Administrator account.
If you manage multiple tenants, retrieve and verify the current context:
powershell$context = Get-MgContext; $contextConnect specifically to this tenant
powershellConnect-MgGraph -NoWelcome -TenantId $context.TenantId -Scopes "Domain.ReadWrite.All User.ReadWrite.All Directory.ReadWrite.All Directory.AccessAsUser.All"
Check the authentication method of your domain
powershellGet-MgDomain -DomainId yourdomain.comIf the domain is federated, review its federation configuration.
powershellGet-MgDomainFederationConfiguration -DomainId yourdomain.com
Retrieve the UserLock SSO signing certificate and save it in a PowerShell variable:
powershell$response = Invoke-RestMethod -Uri "https://<userlock_sso>/api/infos/certificate" -Method GET $certData = $response.currentCertificate.rawCertificateFederate your domain with UserLock SSO
powershellNew-MgDomainFederationConfiguration ` -DomainId yourdomain.com ` -IssuerUri "https://<userlock_sso>/.domain.com" ` -PassiveSignInUri "https://<userlock_sso>/saml/sso" ` -SignOutUri "https://<userlock_sso>/connect/endsession" ` -SigningCertificate $certData ` -FederatedIdpMfaBehavior "acceptIfMfaDoneByFederatedIdp" ` -IsSignedAuthenticationRequestRequired ` -PreferredAuthenticationProtocol saml
To revert your domain to managed authentication, execute the following command:
Update-MgDomain -DomainId yourdomain.com -AuthenticationType ManagedFirst you need to connect to the Graph API
Get-MgUser -UserId user@domain.com -Property "Mail, DisplayName, GivenName, Surname, UserPrincipalName, OnPremisesImmutableId" | select Mail, DisplayName, GivenName, Surname, UserPrincipalName, OnPremisesImmutableIdNote
This method is only ment to be used if you encounter issues with the UserLock SSO Assistant and Microsoft Entra solutions
Create the user in the default domain by replacing the placeholder values in this script (xxx.onmicrosoft.com):
powershell$immutableId = [convert]::ToBase64String((Get-ADUser -Identity <samAccountName>| Select-Object -ExpandProperty ObjectGUID).ToByteArray()) $PasswordProfile = @{Password = 'MySuperStrongPassword' ForceChangePasswordNextSignIn = $false} New-MgUser -UserPrincipalName newuser@office365domain.onmicrosoft.com -DisplayName '<Firstname> <Lastname>' -OnPremisesImmutableId $immutableId -PasswordProfile $PasswordProfile -AccountEnabled -MailNickname <Nickname>Move the user to the federated domain:
powershellUpdate-MgUser -UserId newuser@office365domain.onmicrosoft.com -UserPrincipalName newuser@domain.com
Move the user to the default domain:
powershellUpdate-MgUser -UserId newuser@domain.com -UserPrincipalName newuser@office365domain.onmicrosoft.comAdd the ImmutableId value:
powershell$immutableId = [convert]::ToBase64String((Get-ADUser -Identity <samAccountName>| Select-Object -ExpandProperty ObjectGUID).ToByteArray()) Update-MgUser -UserId newuser@domain.com -OnPremisesImmutableId $immutableIdMove the user back to the federated domain:
powershellUpdate-MgUser -UserId newuser@office365domain.onmicrosoft.com -UserPrincipalName newuser@domain.com