Set up and restrict user access to Wi-Fi sessions
This following example will give you a step-by-step guide on how to restrict users’ access to Wi-Fi sessions with UserLock, using RADIUS Authentication and RADIUS Accounting.
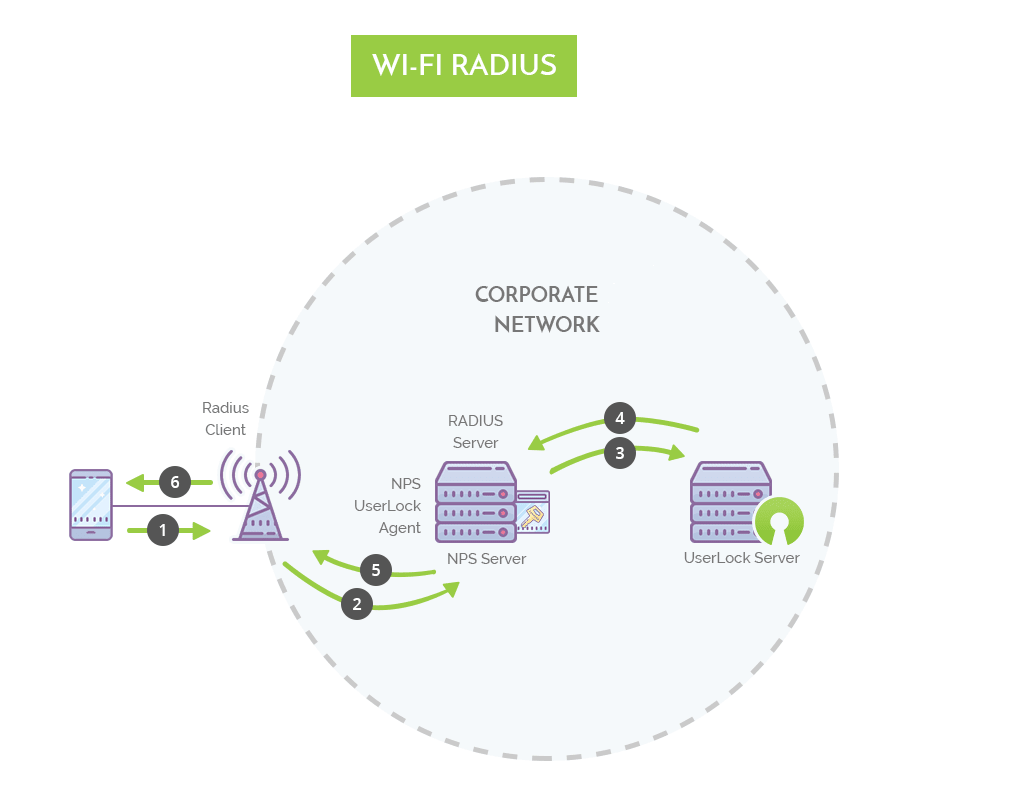
Overview Diagram
Getting Started
Conventions
Note for this example we use the following conventions:
- "NPS" refers to "Network Policy Server" (available for Windows Server 2008 and later editions) or "IAS" to talk about "Internet Authentication Service" (available for Windows Server 2003 and earlier editions).
Requirements
- A Wi-Fi Access Point compatible and configured with RADIUS Authentication and RADIUS Accounting.
- If RADIUS Accounting is not configured, UserLock will not receive logoff notifications, so its data will be incomplete. That's why all instances of RADIUS Accounting are in bold.
- A Network Policy Server (NPS).
Notes
RADIUS (Remote Authentication Dial-In User Service) is a protocol for authentication and accounting. RADIUS Authentication and RADIUS Accounting are two different things, and both are needed to be compatible with UserLock. Usually, RADIUS Authentication is on port 1812 or 1645, and RADIUS Accounting is on port 1813 or 1646.
NPS is the Microsoft implementation of RADIUS from Windows Server 2008. It is the successor of IAS used in editions up to Windows Server 2003.
Wi-Fi is a standard for wireless communications. It is possible to configure RADIUS for Wi-Fi depending on access points. RADIUS Authentication and Accounting are required for UserLock to manage Wi-Fi sessions.
Currently, it is not possible to log off Wi-Fi (and VPN) sessions with UserLock. It is only possible with Interactive (desktop) and IIS sessions.
Configure the Wi-Fi Access Point
Verify that RADIUS Authentication and RADIUS Accounting are configured on your Wi-Fi access points.
Install the NPS UserLock Agent to the NPS Server
-
From the UserLock console, deploy the NPS agent on the NPS server:
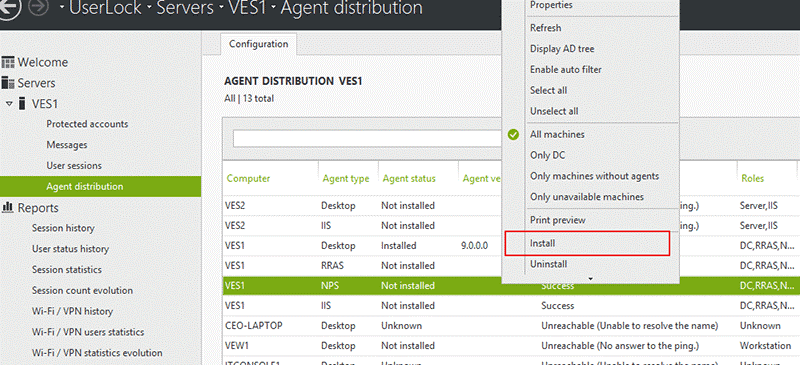
-
Under the NPS server, run CMD (or PowerShell) as administrator and run the following commands (caution: it will disconnect all Wi-Fi connections active at that moment):
- net stop remoteaccess
- net stop ias
- net start ias
- net start remoteaccess
-
From the UserLock Console, check that the status of the NPS agent is "Installed"

Test the protection restricting all users to 1 concurrent Wi-Fi Session maximum
-
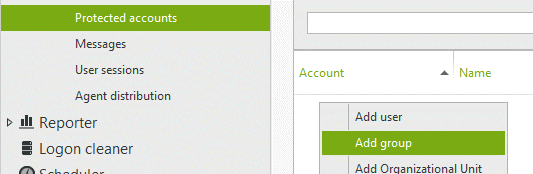
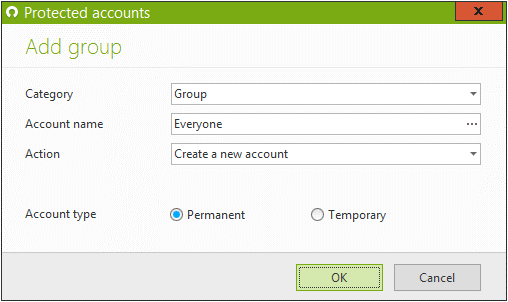
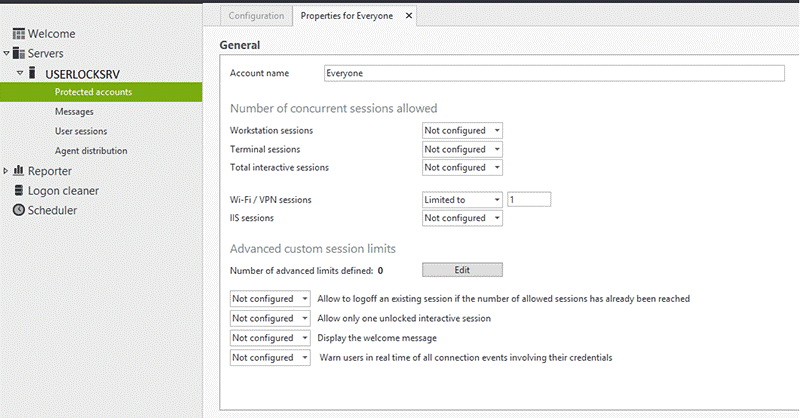
Create a protected account called "Everyone" to apply this new rule to all users.
-
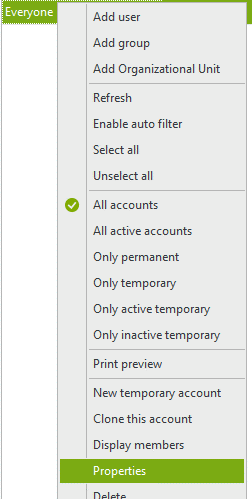
Configure the "Everyone" protected account (selecting “Properties”) to restrict each user to 1 concurrent Wi-Fi session maximum:
Testing the UserLock restrictions
-
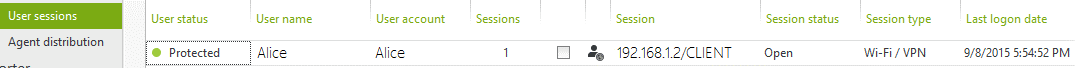
Make a Wi-Fi connection with one account (in this example the account "Alice"). The connection is successful. You can see the session in the UserLock console.
-
Now try opening a second Wi-Fi connection with Alice, it will be denied.
Advanced
Other restrictions you can apply to Wi-Fi connections
Other restrictions are also possible for Wi-Fi sessions: For example by defining working hours, time quotas...
To learn more about all the rules allowing you to define network access conditions, please see the "Protected accounts" help section.
Wi-Fi Authentication mode
UserLock cannot monitor interactive sessions and Wi-Fi sessions for domain computers where the desktop agent is installed.
If the machine is a member of the domain, and the desktop agent is installed, the Wi-Fi must be configured with "computer authentication" for the desktop agent to function correctly.
For machines that are not part of the domain, the Wi-Fi authentication mode must be configured with "user authentication" to monitor Wi-Fi sessions.
Wi-Fi authentication mode can be changed in the properties of the Wi-Fi network adaptor or via GPO.