Scan options
FileAudit allows certain events to be excluded from the audited access events:
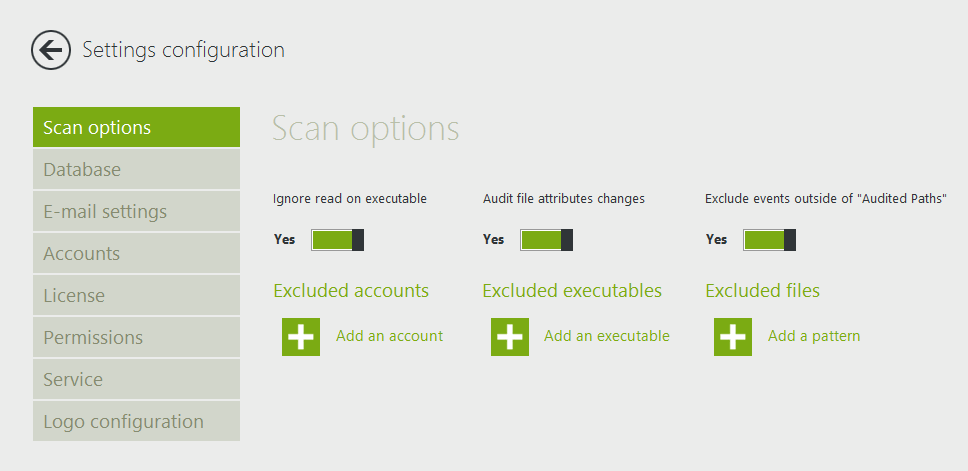
How to add an exclusion.
You can exclude access events generated for specific user accounts, executables and files pattern. Select what type of item is to be excluded (e.g. ‘Add a pattern’), which will activate a panel on the right-hand side. In this panel, type the object you wish to exclude:
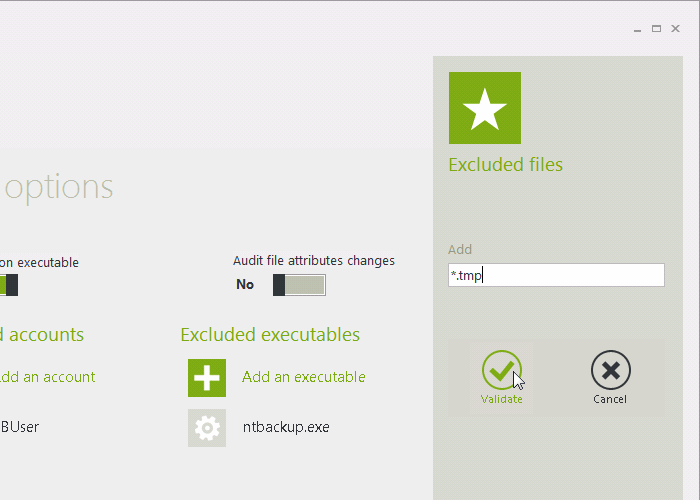
Take note: Wildcards are usable only to define exclusions on file patterns:
* : matches any string.
? : matches any character.
Ignore read on executable
Most executable files load an associated icon image when the file name is listed in Windows Explorer, generating a read access event.
By default, FileAudit ignores this read event to avoid the display of these non-relevant read accesses. This doesn't affect the 'execute' access type.
If for any reason you need to take in consideration a 'read access attempt' of an executable file, just switch off this option.
Audit file attributes changes
FileAudit can audit modifications done on file attributes (Read-only, Hidden, etc...). By default this ability is disabled.
To enable the audit on file attribute changes, just switch it on.
Take note: Once this option is enabled, it is necessary to relaunch the configuration of any existing paths. (Paths that are already registered to be audited - listed in the "Audit configuration" view - will not include the suitable 'NTFS Audit configuration' that is needed to audit the file attribute changes). This is simply done by following the procedure described in the help section "Check the audit configuration". Once done, subsequent paths will integrate the proper configuration without any additional action required.
Exclude events of no audited paths
Unwanted audits can be generated when an NTFS audit manual configuration is in place or because other tool has left their audit configuration. By activating this feature only the paths configured within FileAudit will be audited.