Audit Active Directory user logins
Audit Active Directory user logins without spending hours in Event Viewer or juggling PowerShell scripts.
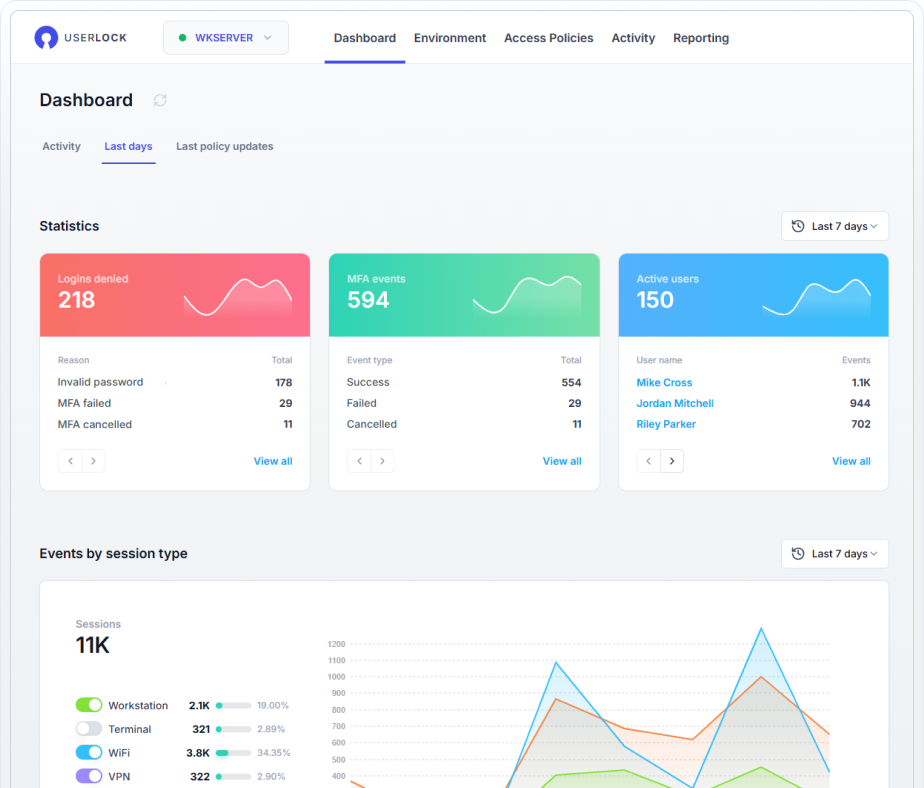
UserLock gives you a centralized, searchable dashboard to track and investigate logon events across your entire AD environment, in real time or historically.
Get accurate insights
Spot suspicious activity
Meet compliance requirements
Auditing user login activity in Active Directory shouldn’t be this hard
Trying to check user login history in Active Directory using native tools is a painful, manual process. Even with Event Viewer and PowerShell, you’re stuck digging through scattered event logs, searching for event IDs, and correlating logon and logoff data across machines.
One user might generate hundreds of entries in a day. Multiply that across users and machines, and you’ve got a bandaid that’s hard to scale and doesn’t offer clear audit logs for compliance reporting.
It shouldn’t take hours of digging to answer a question like “Who logged in, when, how, and from where?”

Get full visibility into Active Directory user login history
Record and report on all user logon events, logoff records, and session data from audited Windows machines. From a single interface, IT can see who accessed what, when, how, and from where, instantly.
View all Windows access events across audited AD machines, users, groups, and organizational units.
Filter by time, session type, user, IP address, and more.
Drill into user logs, session history, and access attempts (successful and denied).
Monitor administrator actions, UAC prompts, and account lockouts.

Smart auditing that adapts to your team’s needs
UserLock is built for how IT admins actually work. Cut through the noise and surface the information you need, fast.
Apply powerful filters to create personalized reports
Save and reuse personalized views tailored to your needs
Schedule and automatically send reports via email
Export reports in multiple formats
Connect to your SIEM via the UserLock API
UserLock stores all audit data in a tamper-proof ODBC database for security and compliance purposes.

Simplify compliance and prove you can audit access
Whether you need to comply with major regulations such as ISO 27001, GDPR, HIPAA, or cyber insurance audits, UserLock helps you demonstrate that you've implemented the necessary access controls are are monitoring access.
Audit:
When users access AD domains
Which machines they connected from
How long their sessions lasted
How many sessions or concurrent logins you allow
When MFA or access policies were triggered
Who attempted (or failed) to log in
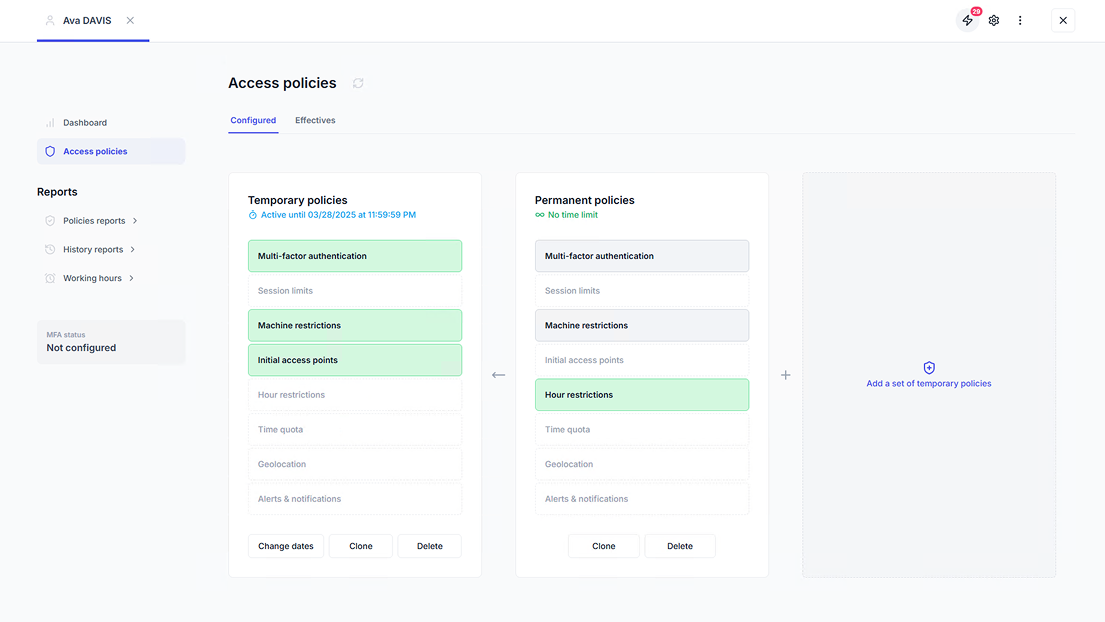
Go beyond auditing, act on what you see
Auditing alone isn’t enough. Audit and act from the same interface, no need to switch tools. UserLock combines reporting with comprehensive access controls to help you prevent unauthorized access and act fast.
Apply granular multi-factor authentication
Enforce contextual access controls
Limit concurrent logins to ensure users are accountable
Monitor access in real-time and set up alerts on anomalies
Block or logoff users in response to suspicious activity