A two-factor authentication solution for Windows & RDP (Remote Desktop) logons
15 reasons why IT pros choose UserLock for strong two-factor authentication (2FA) and contextual access management across all Windows logon, RDP, IIS, and VPN connections.
Updated October 15, 2025)
Two-factor authentication (2FA) with UserLock provides any on-premise or hybrid Active Directory (AD) environment with secure employee access to corporate networks and cloud applications, no matter where they work. As a part of UserLock’s go-to access management solution, it gives you the best of both worlds: a secure network and productive employees.
Simple to implement and intuitive to manage, UserLock 2FA builds on your existing investment in your Microsoft on-premise Active Directory infrastructure. UserLock doesn’t make modifications to your AD accounts, structure or schema, so it offers seamless 2FA for Windows logins.
Choose to enable 2FA on remote connections like Remote Desktop. End-users connecting to another machine (like a remote computer or virtual machine) within the network can still receive a 2FA challenge.
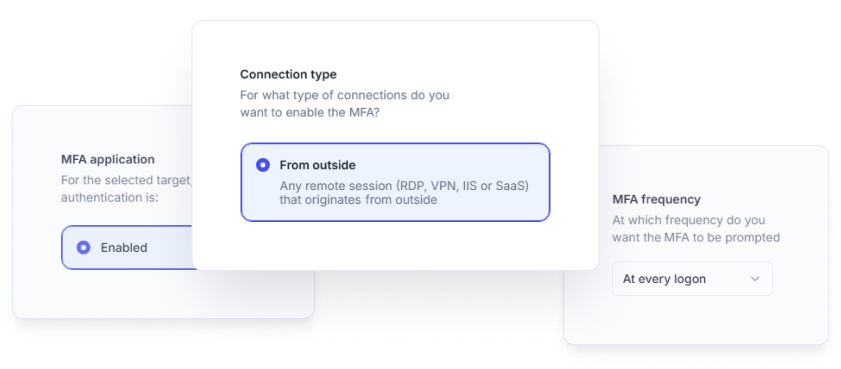
Administrators can choose to either apply 2FA to RDP logons that originate from outside the corporate network, or to every RDP logon — both internal and external.
Remote Desktop Gateway (RDG or RD Gateway) enables network access for remote users via the internet. By utilizing the Remote Desktop and the HTTPS protocol it creates a secure encrypted connection.
RDP connections that pass through a gateway are by default considered as coming from “inside” the network. UserLock also allows you to identify the real IP address of an RD Gateway connection and view these connections as ‘outside’ the network.
You can then choose to enable MFA only for RDP logons that originate outside the network — and be sure to include all RD Gateway connections.
VPNs and IIS sessions are vulnerable to specific security threats, like phishing and spear phishing attacks. After easily installing the UserLock agent on each machine or IIS server that you want to protect, you can easily apply 2FA for VPN as well as 2FA for IIS connections. Since 2FA prevents hackers from accessing your network using compromised credentials, this adds an extra layer of security against unauthorized VPN and IIS access.
Can you secure remote logons, even when your remote employees neither have a VPN nor a connection to the network? This common loophole is often a blind spot for 2FA application. UserLock secures remote connections event when users aren’t connected to the domain, allowing administrators to continue to apply off-domain 2FA, monitor user activity and enforce security policies.
UserLock combines 2FA with single sign-on (SSO) for secure and frictionless access to multiple cloud resources. Employees log in just once, with optional 2FA, using their existing on-premises AD credentials to instantly access resources like Microsoft 365 and cloud applications, from wherever they work.
And since administrators can combine SSO with granular MFA, they control how often they ask for MFA for SaaS apps to balance security with employee productivity.
With UserLock, you can choose between two different 2FA authentication methods: push notifications, authenticator applications or programmable hardware tokens.
Many organizations choose push notifications or an authentication app to balance security, ease of use and cost.
Programmable hardware authentication devices such as tokens or security keys are also a secure, simple way to implement MFA, especially for end-users who don’t have access to a corporate smartphone.
In both TOTP and HOTP, the token (the OTP generator) generates a numeric code. The OTP’s security is based on the fact that the codes are constantly changing (because they’re single use – hence the name!). HOTP works just like TOTP, except that an authentication counter is used instead of a timestamp.
For any user, user group or OU, you can specify when you want to prompt for MFA. Thanks to UserLock's granular MFA controls, you can choose: by connection type, workstation or server connections, and frequency (every connection, every X days, at the first logon of the day, on every new machine).
Here's how admins can choose how often to prompt for MFA, for each session and connection type.
)
)
)
)
)
)
)
Securing access from all users aligns with most organizations’ desire to protect any Active Directory account with access to critical data and resources.
It also improves IT admins’ ability to restrict and respond to the most privileged of accounts: Windows local administrator accounts, Windows domain administrator accounts, and Active Directory service accounts.
For maximum security, UserLock installs directly alongside your organization’s on-premise AD environment. Its Windows domain 2FA can be administered from any workstation remotely, so your whole IT team can get insights, alerts and reports on all 2FA activity across your organization.
From the console, administrators can easily interact with and respond to any session, as well as reset or bypass authentication settings for any specific user.
With UserLock’s contextual restrictions in place, administrators can confidently customize 2FA controls to avoid prompting the user for a second authentication each time they log in.
Transparent to the end-user, these restrictions create a significant barrier to any attacker without impeding employee productivity. They also help administrators distinguish legitimate asks to bypass or to reset 2FA.
UserLock’s contextual factors include location, machine, time, session type and number of concurrent sessions.
UserLock’s 2FA is non-disruptive for both users and IT teams.
For users: Enrollment is intuitive and simple for users to do on their own. IT admins can also choose to give users a set of recovery codes, so users can easily regain access in case they don’t have their cell phone or security key. Alerts also warn end-users when their own credentials are used (successfully or not), empowering users to take responsibility for their own trusted access.
For IT teams: Help requests alert administrators in real-time, allowing them to immediately, easily respond with one-click actions, and allowing users to get on with their job.
UserLock offers a comprehensive on-premise 2FA solution that works even without internet access. This means that secure authentication for your employees is possible from just about everywhere.
Read how one client uses offline MFA to secure global employee access to user sessions and to the corporate environment.
2FA doesn’t have to come at a high cost, but it does have to be effective. UserLock offers enterprise-caliber 2FA that’s focused and effective, but SMB-friendly in its ease of use and implementation.
2FA is one of UserLock’s access security and management capabilities that work together to verify Active Directory identity access to network and SaaS resources.
Two-factor authentication (2FA): Secure two-factor authentication on Windows logon, RDP and RD Gateway, VPN, IIS, VDI, and SaaS connections. Define the circumstances to verify the identity of all users, using one-time passwords.
Single sign-on (SSO): Combined with MFA and session management, UserLock’s secure SSO gives employees seamless, secure access to SaaS resources based on the strong on-prem AD identity authentication.
Contextual access policy & restrictions: Restrictions can be established to limit when an account can logon, from which machines, devices or IP addresses, using only approved session types (including Wi-Fi, VPN and IIS) and number of concurrent sessions, etc. helping to reduce the risk of inappropriate use.
Real time monitoring & reporting: Every logon is monitored and tested against existing policies to determine if a logon should be allowed. Full visibility gives insight into any anomalous account behavior that may indicate a potential threat. Reporting helps ensure detailed insights for any investigations.
IT and end-user alerting: Notifies IT and the user themselves of inappropriate logon activity and failed attempts.
Immediate response: Allows IT to interact with a suspect session, to lock the console, log off the user, or even block them from further logons.
)
)
)