Comprehensive guide to Windows domain 2 factor authentication (2FA)
Securing access to your Windows domain is paramount. Implementing Windows domain 2 factor authentication (2FA) with Active Directory not only bolsters security but also ensures compliance. With UserLock, deploying 2FA is streamlined and effective, protecting access across all session types including RDP, VPN, IIS, and SaaS.
Updated December 16, 2025)
Windows domains and Active Directory (AD) makes it easy for administrators to control a large number of business PCs and devices from a central location. Today, a huge percentage of enterprises continue to rely on Windows domain AD to manage assets, users, systems, policies, profiles, and rights. Given that, it’s increasingly important to protect user account access with Windows domain 2-factor authentication.
Why? Even after all these years, the consistency, centralized management, and scalability of a Windows domain mean it continues to live at the center of a company’s IT infrastructure, but it doesn’t mean it can’t be enhanced.
Take the security of Active Directory user credentials. According to the Verizon Data Breach report, lost or stolen credentials are the number one way attackers gain access to systems. Using only a strong user name and password doesn’t cut it anymore. Your Active Directory password can be cracked in 5 minutes or less!
UserLock allows you to protect your Windows domain AD with Windows domain two factor authentication (2FA) and contextual access restrictions.
See how UserLock 2FA works
UserLock solves for the identity security gaps and vulnerabilities your organization has today. Because even though cloud adoption is moving fast, moving an organization from full on-prem to full cloud doesn't happen overnight. Some organizations may never make that journey at all, and will stay on prem by choice or to meet regulatory requirement.
Regardless of where your organization falls there, our unique approach puts the focus on securing critical on prem AD identity access first. Then, we extend secure on prem authentication with MFA and SSO for secure cloud access.
Other solutions start with the cloud, then move backwards to secure on prem.
But you want your attack surface to stay as small as possible, for as long as possible. Usually, that means keeping critical systems, legacy apps, and authentication workflows on prem.
Schedule a personalized demo
See how UserLock fits your needs and explore common use cases
Enabling 2FA for endpoints across a Windows AD domain can be challenging without the right tools (usually third-party 2FA software). As businesses extend their IT architecture beyond traditional security perimeters, the reliance on Remote Desktop (RDP) connections and Virtual Private Network (VPN) access grows. UserLock solves for the security needs of the environment you have today: one that's likely based on-premise, but also includes remote access and access to cloud SaaS applications and web-based services.
First, UserLock does this by providing a seamless 2FA integration with Active Directory.
UserLock's constant communication with AD sets it apart from other MFA solutions, where on-premise AD compatibility is often added on vs. by design.
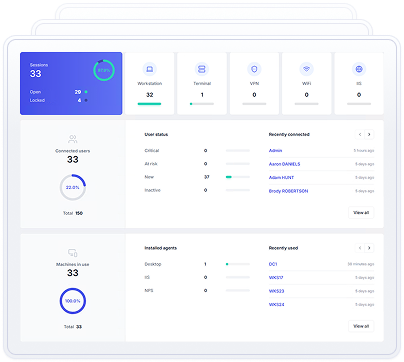
With UserLock, synchronization with your on-premise AD happens in real time, and you can also get visibility on your AD environment directly from the console.
This close connection with AD also allows you to apply MFA granularly.
There are three different ways UserLock allows you to apply MFA granularly: by protected account, by frequency, and by session type.
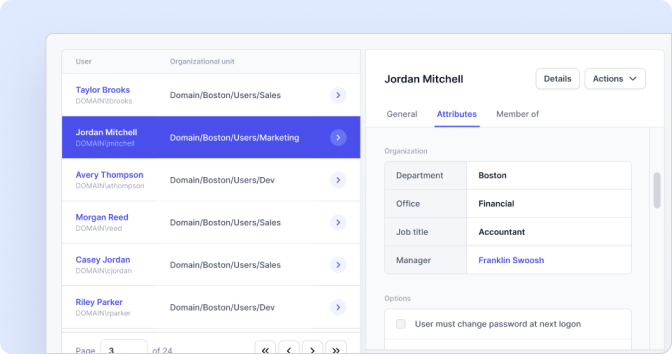
First, you can set UserLock's MFA and access control policies according to your existing AD users, groups, and OUs.
Second, you can choose to apply MFA by connection type (all, remote, from outside the network, not configured) and by session type (Workstation, Server, IIS, VPN, SaaS).
Third, you control MFA prompt frequency so you balance productivity and security for your team's unique needs.
)
)
)
)
)
)
)
And, UserLock is the only 2FA solution today that allows you to protect all connection types, without taking authentication away from your on-premise AD. This means you can apply security across commonly vulnerable connection types, including 2FA for VPN, RDP MFA, and MFA for Microsoft 365 and SaaS apps. All with one tool, one centralized audit, and the skills your IT team already has.
)
)
)
)
)
)
)
With UserLock, 2FA for endpoints is very easy across all session types, including Windows domain logins, Remote Desktop (RDP, RD Gateway and RD Web, RemoteApp), OWA, VPN, and SaaS.
To start, it’s easy to deploy UserLock software right alongside Active Directory and distribute a light agent across all devices you want to protect. An automated deployment engine makes it easy even for larger user bases. (With no modifications to AD accounts, its structure or its schema.)
Next, simply look-up and add Active Directory users via a wizard. You don’t have to add accounts individually; you can look-up and add Active Directory groups or organizational units that you want to protect with 2FA.
Once you’ve enrolled a user in 2FA, the user will receive a prompt on their next login to install an authentication application or to use a hardware-based token, such as YubiKey or Token2. At subsequent logins requiring 2FA, users will first enter their password, then receive either a push notification or a prompt with a dialog box for a validation code.
To determine exactly how, when, and where to prompt the user for a second factor, administrators define granular circumstances for just one individual or easily scaled across groups of users.
Admins can set up how much time users have to complete self-enrollment. While the process is extremely simple, a flexible on-ramp gives users the opportunity to “ask for help” from an administrator any time during the process.
So, in just a few short steps, you can add Windows domain two factor authentication bolsters security across your network.
In addition to 2FA, UserLock also offers a comprehensive suite of security layers to better protect login access.
You can configure device restrictions, time restrictions, and geolocation restrictions or even limit the number of simultaneous connections.
How to set up contextual access policies
These type of contextual access restrictions offer customized policies beyond what is natively capable in Active Directory, to further protect login credentials and help avoid prompting the user for 2FA each time they log in.
An extremely powerful part of UserLock's Windows 2FA solution is also the visibility, auditing, and reporting that you get. You instantly see how and when users connect to your network.
)
)
)
)
)
)
)
You also see a risk indicator next to each session to easily detect risks, and can set up alerts on how they behave throughout various login sessions.
If you find suspicious activity on any specific account, an administrator can choose to block the user or close certain connections that a user may currently have, directly from the UserLock console.
By choosing UserLock for your Windows Domain 2 factor authentication needs, you not only enhance security and gain peace of mind, but you also lean into the AD skills your IT team already has. In today's tight market for IT recruitment, this makes UserLock even more cost-effective.
Protect your organization from phishing scams and unauthorized access. Try UserLock today and experience superior security purpose-built for securing your Windows domain.