File access event alerts and automated response
Customize alerts and respond to specific file audit events, such as access denied, file deletion, specific user activity, unusual access times, or mass actions like copying, deleting, or moving large volumes of files.
Real time alerts on Windows file audit events
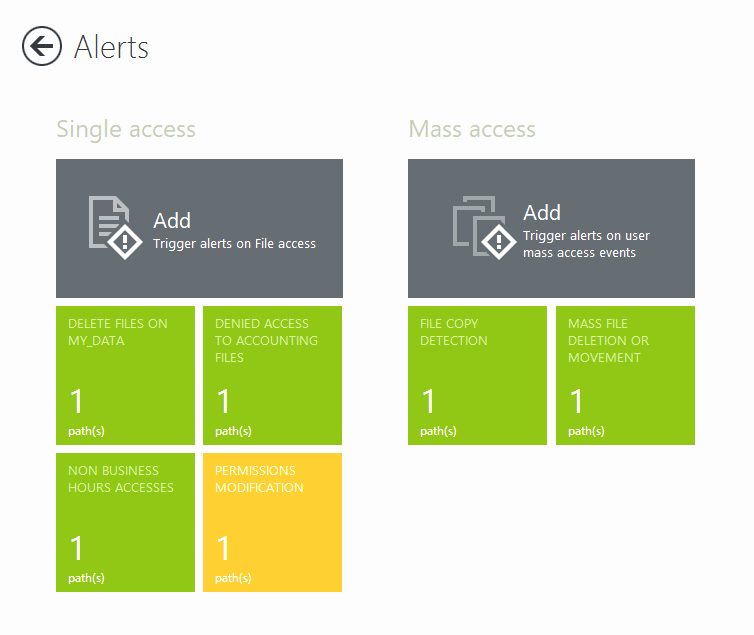
Single access events
Get alerts on events such as file deletions, access denials, or activity from specific users, machines, or IP addresses. React quickly or run scripts to trigger automatic responses.
Mass access events
Set threshold alerts for bulk file copying, deletion, or movement detected by FileAudit. Run predefined scripts to stop threats like ransomware.
Customize alerts based on specific criteria
See your alert history report for clear visibility and issue spotting.
File and Folder
Access & Object Type
Access & Object Type
Access Time
Access frequency
Machine Name & IP Address
Process Name
Recipient
Set alerts on access events on-premises and in the cloud
Access events with an * are available only for certain cloud storage providers.
Read
A user tried to open a file in ‘Read’ mode
Write
A user tried to modify a file or folder
Delete
A user tried to delete a file or folder
Move *
A user moved a file to another directory
Execute
A user tried to execute an executable file
Write attributes
A user tried to modify a file attribute (E.g. Read only or Hidden Checkboxes)
Ownership
A user tried to take ownership of a file or folder
Permissions
A user tried to change the permissions on the file or folder
Rename
A user renamed a file
Copy *
A user copied a file
Create *
A user created a new file
Shared *
A user shared a file to another user
File access alerts for cloud based storage
FileAudit can extend alerting to activity in major cloud-based file storage providers.
Get visibility on
Microsoft OneDrive for Business
Microsoft Teams
SharePoint Online
Google Drive
Dropbox Business
Box
Receive alerts on bulk file copy, deletion, or movement
FileAudit monitors how often a user accesses specific files or folders. A mass access alert is triggered when activity exceeds a defined threshold within a set period.
Different mass access types
Alerts display the username, source, date, time, and alert criteria. This makes it easier to investigate the full access history in FileAudit.
Bulk file copying
When a large number of read accesses happen within a short period, it's a strong indicator that the user has performed a copy/paste operation.
Bulk file deletion or movement
When many deletions happen within a short timeframe, it usually means the user has deleted or moved multiple files.
Alerts on irregular access time
When configuring alerts in FileAudit, administrators can factor in the day and time of access. Alerts will then only trigger if access happens outside the specific time window. For example, outside of normal working hours.
This helps lower the risk of inappropriate or suspicious access while avoiding unnecessary disruptions to administrators and users.
Automatic responses to file access alerts
Go beyond real-time monitoring and alerts. Take immediate action on potential threats without waiting for IT to intervene.
Set up predefined or custom PowerShell scripts to automatically respond when an alert is triggered.
Shut down a machine, log off a user, and act before any damage is done.

Smarter, faster, more efficient file auditing
Set up alerts for successful or unsuccessful access attempts, or both
Get email alerts, and view a filterable alert history report
FileAudit goes beyond logs and visibility. You can actively elevate data security across a hybrid organization with real-time alerts and automatic responses.
Secure your organization against improper access, potential theft, modification, or deletion of sensitive files and folders.