Beyond passwords: how the Tycoon 2FA phishing kit works
Tycoon 2FA phishing doesn't just bypass the logon, it exposes post-authentication as the real battleground.
Published April 30, 2026)
Tycoon 2FA phishing techniques allow attackers to bypass the login entirely. While stopping these types of adversary-in-the-middle (AiTM) attacks is challenging, carefully implemented multi-factor authentication (MFA) and access controls help contain the risk of MFA bypass attacks.
In 2023, a new adversary-in-the-middle (AiTM) phishing platform called Tycoon 2FA emerged, challenging this assumption. It turned out that while attackers couldn't bypass MFA itself, using Tycoon MFA, they could do the next best thing: steal session tokens.
Users log in by entering the correct password and MFA when prompted to do so. However, thanks to the stateless design of HTTP, what keeps them logged in is the cryptographic session token wrapped inside a cookie. Without this small convenience stored on a device, users would have to continuously re-authenticate on every page load or API call.
The possibility that adversaries might steal these session tokens or cookies has been known for some time. Sold as Phishing-as-a-Service (PhaaS), Tycoon 2FA's innovation was to make achieving this much easier for non-expert attackers.
Outwardly, a Tycoon 2FA attack operates in the same way as any phishing attack: a user receives a convincing-looking phishing email containing a malicious link or QR code.
Clicking on the link takes the user to a fake login page (using templates generated in real time from genuine Microsoft 365, Gmail business, or a cloud account login).
Victims logging in are routed via a reverse proxy (the "adversary in the middle"), which sits between the user and the real domain.
The login and authentication process look normal. The proxy forwards the password to the genuine login site, sending back the MFA request. When the user enters this, this too is forwarded to the genuine site.
At this point, the genuine site sends back a session token inside a cookie, necessary for user persistence.
The attacker intercepts the session token/cookie bound to the legitimate credential and MFA. Injected into the attacker's browser, this allows them to appear valid to the server, circumventing the need for password/MFA authentication for as long as the token remains valid.
How long this session token lasts will depend on how token expiration has been configured by the server, but could be anything from hours to days. Until that expiration, attackers are free to exploit the compromised account.
The first lesson of Tycoon MFA is that while MFA hugely improves password credential security, it is not invulnerable.
MFA is a principle implemented through several distinct technologies, some of which are more secure than others. But the more secure an MFA technology is, the less convenient it becomes, which forces defenders to compromise. Session tokens with longer expiration times are an example of this.
The only technology able to resist MFA bypass attacks, such as AiTM, is phishing-resistant MFA.
When MFA is set up to work with a hardware token or passkey, the correct domain is bound to the credential using public key cryptographic origin binding. No other domain, including the AiTM proxy phishing domain, will work.
This is phishing's big weakness: the victim must be lured to a bogus domain for an attack to initiate. Phishing-resistant MFA solves this problem by cryptographically binding authentication keys to the legitimate origin, making authentication attempts from a fraudulent domain impossible.
Unfortunately, phishing-resistant MFA has some downsides. Hardware tokens are expensive and can be lost by users, at which point a reset is needed to avoid a lockout. This process introduces new vulnerabilities of its own that attackers can target.
WebAuthn and passkeys provide a solid response to these limitations. However, their support still varies across platforms and devices, and their integration with technologies like VPN or RDP requires additional configuration.
In March 2026, Tycoon MFA's reign over MFA was halted in a joint operation between Europol, Microsoft and other security vendors that saw the seizure of 300 domains used to provide the PhaaS platform to its estimated 2,000 customers.
Nevertheless, because the tools and techniques used by Tycoon 2FA have been adopted by other MFA bypass phishing platforms that have appeared since 2023, the benefits of this are likely to be short-lived.
Phishing systems such as Tycoon 2FA remind us that all authentication systems, including MFA, are prone to failure, misconfiguration, or novel attacks.
For decades, passwords seemed as if they were enough before this started to collapse as attackers worked out how to steal them. MFA is a big improvement on passwords alone, but the technology still often relies on the exchange of data which can be stolen or spoofed.
Phishing-resistant MFA offers strong protection, but even this layer can fail under certain circumstances. In short, no authentication system is foolproof.
This raises a fundamental question: assuming MFA bypass attacks are likely to become a standard technique at some point, is MFA still sufficient?
Right now, the priority for defenders should be to minimize their attack surface. UserLock supports this in a variety of ways.
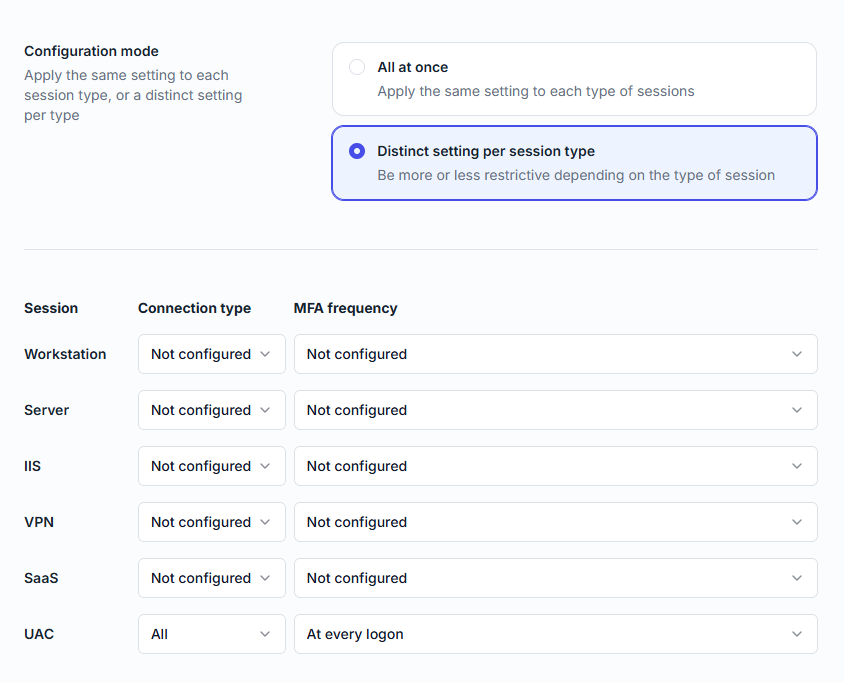
With UserLock, IT can apply MFA on Windows UAC prompts. This adds an identity check at key point where attackers will attempt to elevate privilege.
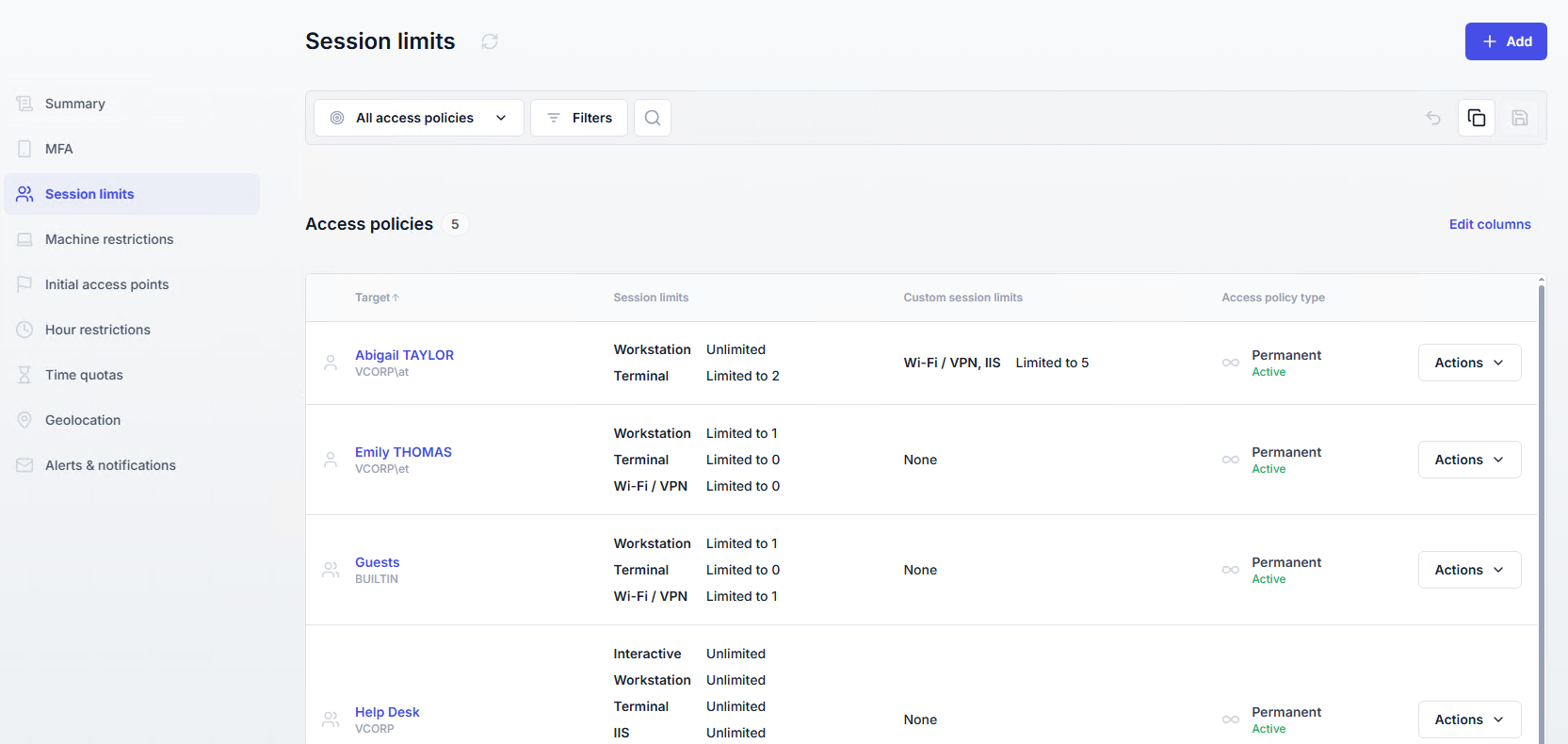
UserLock also allows IT to implement post-authentication access controls. This includes locking down concurrent access by user or organizational unit (OU).
If an attacker tries to use the stolen session token, the system will see this access as a concurrent session and block it. While this doesn't stop attackers from using the session token when the real user logs off, it forces them to wait. If attackers try to reuse a session token while the real user is logged on, this will generate an alert.
UserLock also allows IT to apply contextual access controls such as IP address, time, device, and geographical restrictions.

Admins can set up time-outs for inactive sessions and apply a maximum session length before a new authentication is required. Taken together, these limit an attacker's ability to move freely even if they have a valid session token.
Critically, even where MFA bypass attacks can't be stopped, that doesn't mean they are not detectable after authentication has taken place.
UserLock's strength is that it operates as a protection layer for Active Directory (AD) itself and not only the authentication process. This means it can monitor how accounts are behaving, including when a possibly compromised account attempts to move laterally or elevate its privileges.
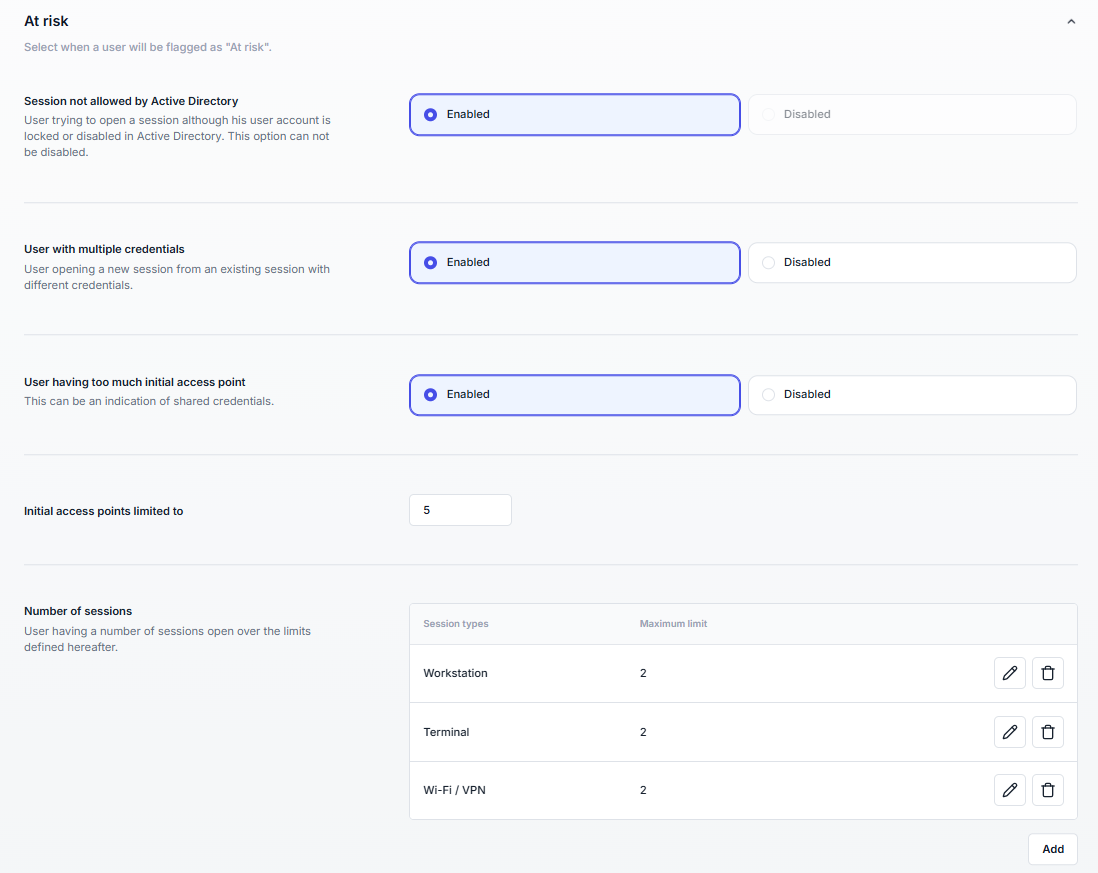
This underlines that while a Tycoon 2FA bypass attack can't be stopped in every case, it is still possible to detect activity of a compromised account post-authentication.
As every attacker knows, compromising an account and bypassing MFA is not enough on its own. They must also move deeper into the network to reach important systems, which in the case of an on-premises network, will be Active Directory.
This is where monitoring the account behavior becomes critical. Even if attackers manage to bypass MFA, there are still network controls that make it possible to detect suspicious behavior.
Tycoon 2FA can spoof authentication, but it doesn't make attackers invisible. Stopping AiTM attacks is challenging but possible. Through carefully implemented user access controls, the risks of MFA bypass attacks can still be contained.
)
)
)