Windows Group Policy for login security
Windows Group Policies can be tedious to configure for logon and access policies. Here's how UserLock takes the strain out of administering and securing login access.
Published August 23, 2019)
Admins often choose Windows Group Policy as the tool of choice to administer Active Directory (AD) user accounts. But managing logon and access policies with Group Policy is time consuming and needs regular maintenance, which can be a challenge for small and medium-sized business (SMBs) with limited on-site IT expertise.
All business, including SMB’s, must be looking to protect confidential data from unauthorized access, particularly with Europe's GDPR (General Data Protection Regulation). Many businesses could see their reputations left in tatters if they fail to shore up their defenses and are hit with GDPR fines.
UserLock simplifies these processes with multiple security layers, clear visibility, and built-in reporting.
Implement multi-factor authentication (MFA)
Manage access policies differently for different session types
Control workstation access
Monitor sessions in real time
Audit and report on access events
Agent deployment is a breeze, and management overhead is nearly zero. Plus, UserLock pricing is clear and transparent. Each subscription license is fully featured and includes technical support, to ensure accurate budgeting and affordability for SMBs and enterprises alike.
With UserLock, connection rules and restrictions can be applied to AD user and administrator accounts, groups, and OUs and you can create temporary time-limited accounts for guests and contractors.
Rules are extremely versatile as you can set the number of initial access points to control points of entry into the network and concurrent user account logins. This is something AD and Group Policy are notoriously lacking in. The elderly LoginLimit tool was updated recently to support Windows 2012 R2 AD servers but is only capable of blocking all concurrent sessions.
IT can set controls to:
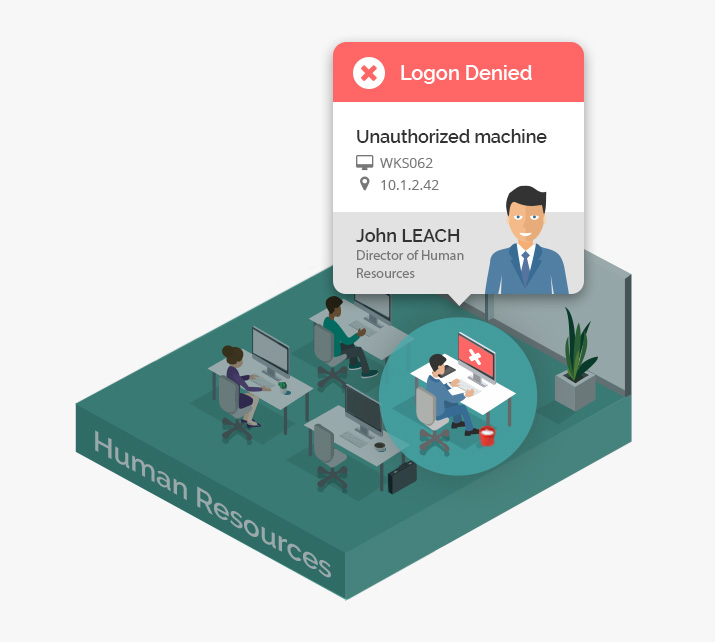
Restrict user logon by device and IP address ranges
Enforce maximum session length and apply time quotas.
UserLock's security policies allow IT to implement granular, lightweight controls. For global rules, admins can set policies at AD group and OU levels. For specific controls, IT can set individual policies by AD user.
UserLock also helps improve user security behavior, awareness, and helps stop password sharing in the workplace. IT can warn users if their account is being used to logon to another computer. If this happens, they’ll receive a pop-up message showing the computer in use and advising them to contact their administrator who will also receive an email alert from UserLock.
UserLock administrators can also interact with selected sessions by clicking on them in the console and logging users off, locking the workstations and resetting them. The blocking feature means you can instantly block a user and stop them reconnecting to any system while we investigated their activities.
AD user logon/logoff reports are available for logon and logoff activities, logons denied by AD and UserLock, failed logins and concurrent session history. They can be scheduled to run at regular intervals or triggered by an event and exported to a range of formats including PDF, XLS, CSV, and HTML. Reporting is easily good enough to satisfy GDPR compliance and external auditors.
According to IT Security Guru's technical review of UserLock:
"UserLock takes the strain out of administering AD user login access. An important differentiator of UserLock is it complements AD and requires no modifications to its schema. It is the perfect access security partner for Windows Active Directory environments."
IT Security Guru
When it comes to managing access, group policy settings are not only tedious to configure but in fact, fail to ensure a user really is who they say they are. Each Windows securiyt gap represents a hole that puts your organization at risk. To ensure a user really is who they say they are, turn to more effective controls.
)
)
)