Network security insider threat: Implement CERT best practices with UserLock
Find out how UserLock helps organizations implement several CERT best practices to mitigate network security insider threats.
)
)
)
)
)
Network security insider threats are influenced by a combination of technical, behavioral and organizational issues. Addressing the threats involves a layered defense strategy consisting of policies, procedures and technologies. UserLock is one such unique technology solution that helps organizations implement many CERT best practices to mitigate insider threats.
The Common Sense Guide to Mitigating Insider Threats
The Common Sense Guide to Mitigating Insider Threats provides the most current recommendations from the CERT® Program, part of Carnegie Mellon University’s Software Engineering Institute, based on an expanded database of more than 700 insider threat cases and continued research and analysis.
Meet these CERT best practices with UserLock
Insiders can be stopped, but it is a complex problem. Focusing on IP theft, IT sabotage, and fraud, this fourth edition of the guide describes 19 practices that organizations should implement across the enterprise to prevent and detect insider threats.
To secure a Microsoft Windows Active Directory infrastructure, UserLock takes security controls beyond native Windows functionality by securing and restricting user access according to customized company policies. Here we look at the CERT best practices that UserLock can help an organization implement.
CERT insider threat best practice #2: Clearly document and consistently enforce policies and controls
“A consistent, clear message on organizational policies and controls will help reduce the chance that employees will inadvertently commit a crime or lash out at the organization for a perceived injustice.”
UserLock allows an organization to notify all users prior to gaining access to a system with a tailor-made warning message.
These messages can for example include:
A tailor-made legal disclaimer, including acceptable use of organization’s systems, information, and resources
last workstation logged onDate and time of last successful logon
History of all logons denied by UserLock and Windows since last successful logon
Number of logons denied by UserLock and Windows since last successful logon
CERT insider threat best practice #4: Monitor and respond to suspicious or disruptive behavior
“Organizations should proactively deal with suspicious or disruptive employees to reduce the risk of malicious insider activity”
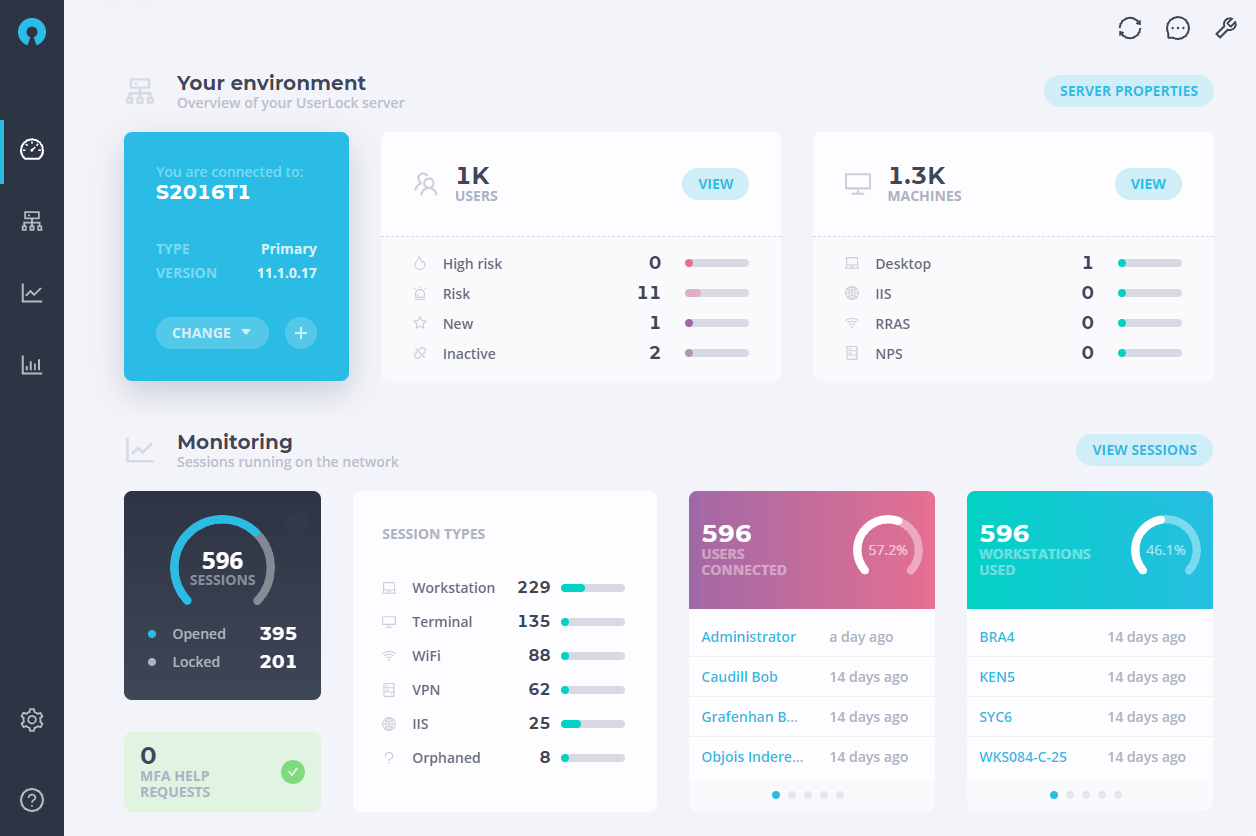
UserLock allows you to monitor in real-time all sessions on your network and to immediately respond to suspicious or disruptive behavior. In case of such behavior, administrators can remotely lock, logoff and reset sessions.
CERT insider threat best practice #3: Implement strict password and account management policies and practices
“If the organization’s computer accounts can be compromised, insiders can circumvent manual and automated control mechanisms. Fine-grained access control combined with proper computer account management will ensure that access to all of the organization’s critical electronic assets is attributed to individual employees.”
Logins are the first line of defense of a network. UserLock provides and enforces granular rules and policies to control and secure network access.UserLock allows:
Limit or prevent concurrent logon (same ID, same password), per user or user group, thus reducing the ability of users to share their credentials and preventing accountability and non-repudiation issues
Define working hours and/or maximum session time for protected users. Outside of this timeframe(s) and/or when time is up, users are disconnected with prior warning
Limit users to their own workstation, department, floor, building etc., through user group network access restrictions
CERT Insider Threat Best Practice (#12): Use a log correlation engine or security information and event management (SIEM) system to log, monitor, and audit employee actions
“Security and logging capabilities have reached the point where data overload is as challenging a problem as data collection. Simply logging all online events is not sufficient to protect an organization’s infrastructure from malicious activity.”In addition to real time session surveillance and monitoring, UserLock records all session logging and locking events in an ODBC database (Access, SQL Server, Oracle, MySQL …) and gives IT administrators the ability to support accountability, legal investigations, and internal trends analysis.
If an IT security breach occurs, UserLock will provide accurate, detailed information about who was connected, from which system(s), since what time, for how long, etc.
Reports can automatically be generated at regular intervals, in order to update an Intranet Web site, or being sent by Email.UserLock provides predefined reports, including:
Session history: Comprehensive session list (logon, lock, logoff instances, users, domains, workstations…)
Session statistics: Displays for a given user and period, total sessions, total connection time, average time per session, per worked day or per week
User sessions: Instantaneous view of all user session at display time.
CERT Insider Threat Best Practice (#14): Deactivate computer access following termination
“Organizations need a termination procedure that reduces the risk of damage from former employees. Termination procedures should ensure that the former employee’s accounts are closed.”
With UserLock, an Active Directory administrators can within seconds remotely lock, logoff and reset all sessions, either from the administration console or the Web interface.
Windows native features will not prevent an employee from logging onto their workstation even if their account has been disabled and deleted.
Fill gaps in Windows native login controls with UserLock
Windows has more security features than any other operating system. But it strangely lacks the fundamental and classic login session controls found in other environments, such as mainframe and midrange systems UNIX and Netware.
This set of articles go deeper into what's lacking in Windows Login Controls and how UserLock fills the gaps in native Windows limitations:
By filling these security gaps, UserLock helps you secure your Windows infrastructure and mitigate insider threats.